Have I Been Pwned is my go-to guy when it comes to checking whether a password has been exposed in any data breaches before. I just go there, punch in the password I’d like to check and click the pwned? button. And you will get the result right away.
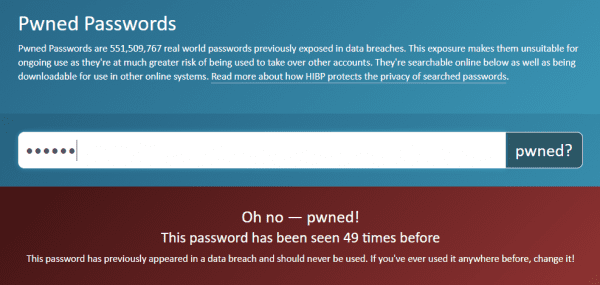
Or, even better, since Have I Been Pwned provides an awesome API for anyone to build an app to quickly search the list of pwned accounts via a REST service, we can craft up a PowerShell script to streamline the process.
Here are the steps how to achieve this:
- Input a password and create a hash of it.
- Send the first 5 bytes of the hash to the API.
- Get the full list of hashes that start with these 5 bytes.
- Check whether one of them on the list matches your full password hash.
One thing to note that since you are only sending the first 5 bytes of the hash over the internet you don’t compromise your hash because of the checking process.
# input password to hash
Add-Type -AssemblyName Microsoft.VisualBasic
$password = [Microsoft.VisualBasic.Interaction]::InputBox("Password to test" , "Password Checker", "")
# get password hash
$stream = [IO.MemoryStream]::new([Text.Encoding]::UTF8.GetBytes($Password))
$hash = Get-FileHash -InputStream $stream -Algorithm SHA1
$stream.Close()
$stream.Dispose()
# find first five and subsequent hash characters
$prefix, $suffix = $hash.Hash -split '(?<=^.{5})'
# ask for matching passwords with the same first 5 hash digits
$url = "https://api.pwnedpasswords.com/range/$prefix"
$response = Invoke-RestMethod -Uri $url -UseBasicParsing
# find the exact match
$lines = $response -split '\r\n'
$seen = foreach ($line in $lines)
{
if ($line.StartsWith($suffix)) {
[int]($line -split ':')[-1]
break
}
}
if (!$seen ) {$seen = "0"}
"The password '$Password' has been seen {0:n0} times." -f $seen You can also download below if you like.
When you launch the code, an Input box will pop up first where you can type in the password you’d like to check.
Further more, you can convert the script into a function and embedded into your own script to check a large chunk of hashes you exported from your own list.
Finally, I have to give the credit to PowerTips for this awesome tip, though I altered the code a bit for a better input and output.